What You’ll Accomplish
Access Control lets you restrict which users can see and use specific connections. Instead of giving everyone access to everything, you can:- Limit production database access to senior engineers
- Give read-only access to analysts
- Restrict sensitive systems to specific teams
- Automatically sync permissions from your identity provider
How It Works
Access Control uses groups to manage permissions. Users belong to groups, and connections are configured to allow access from specific groups.Example
| User | Groups | Can Access |
|---|---|---|
| Alice | engineering, senior | prod-db, staging-db, dev-db |
| Bob | engineering | staging-db, dev-db |
| Carol | analytics | analytics-db (read-only) |
| Dave | support | support-db |
Quick Start
Prerequisites
To get the most out of this guide, you will need to:- Either create an account in our managed instance or deploy your own hoop.dev instance
- You must be your account administrator to perform the following actions
- Groups configured in your identity provider
- Admin access to configure connections
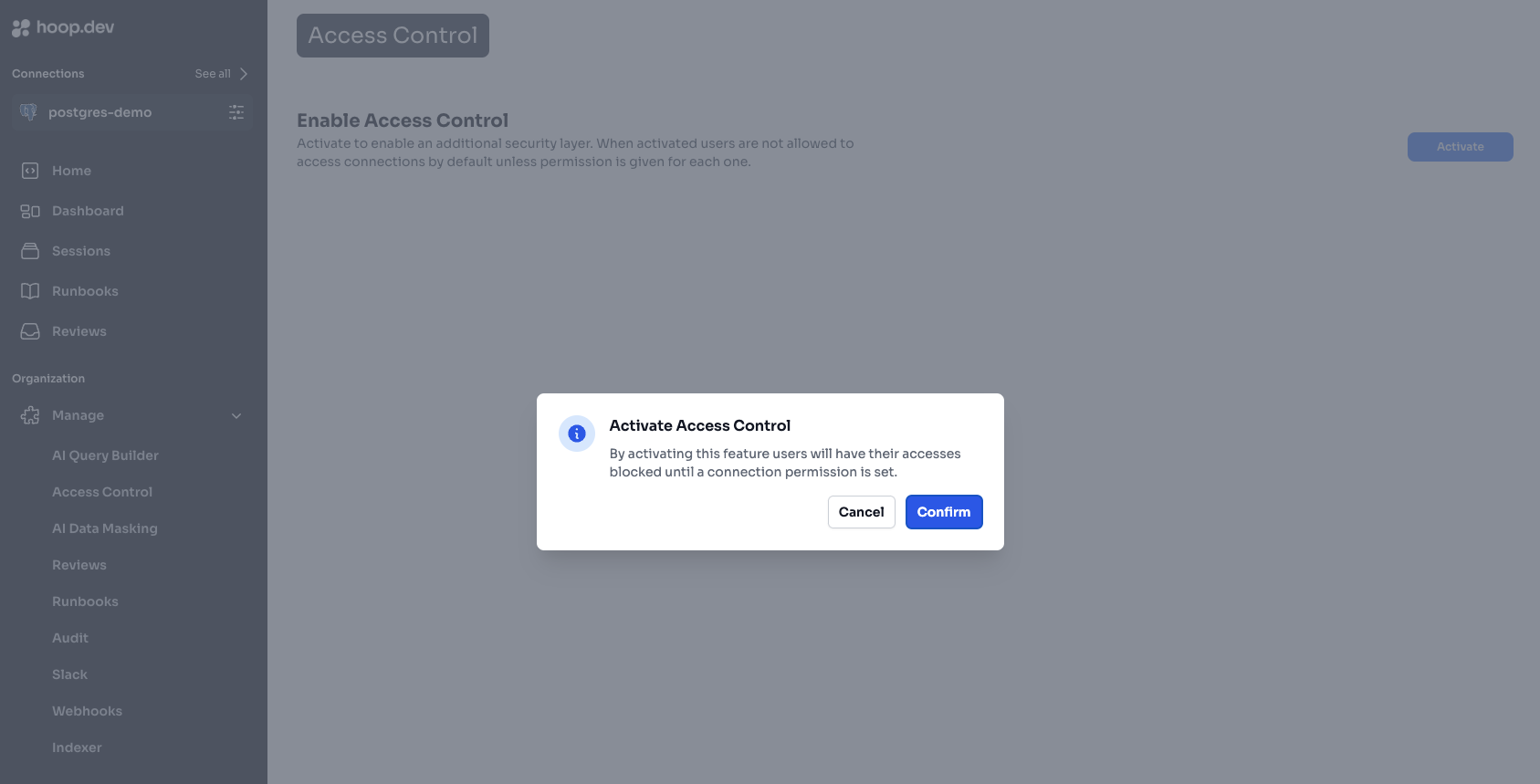
Step 1: Enable Access Control
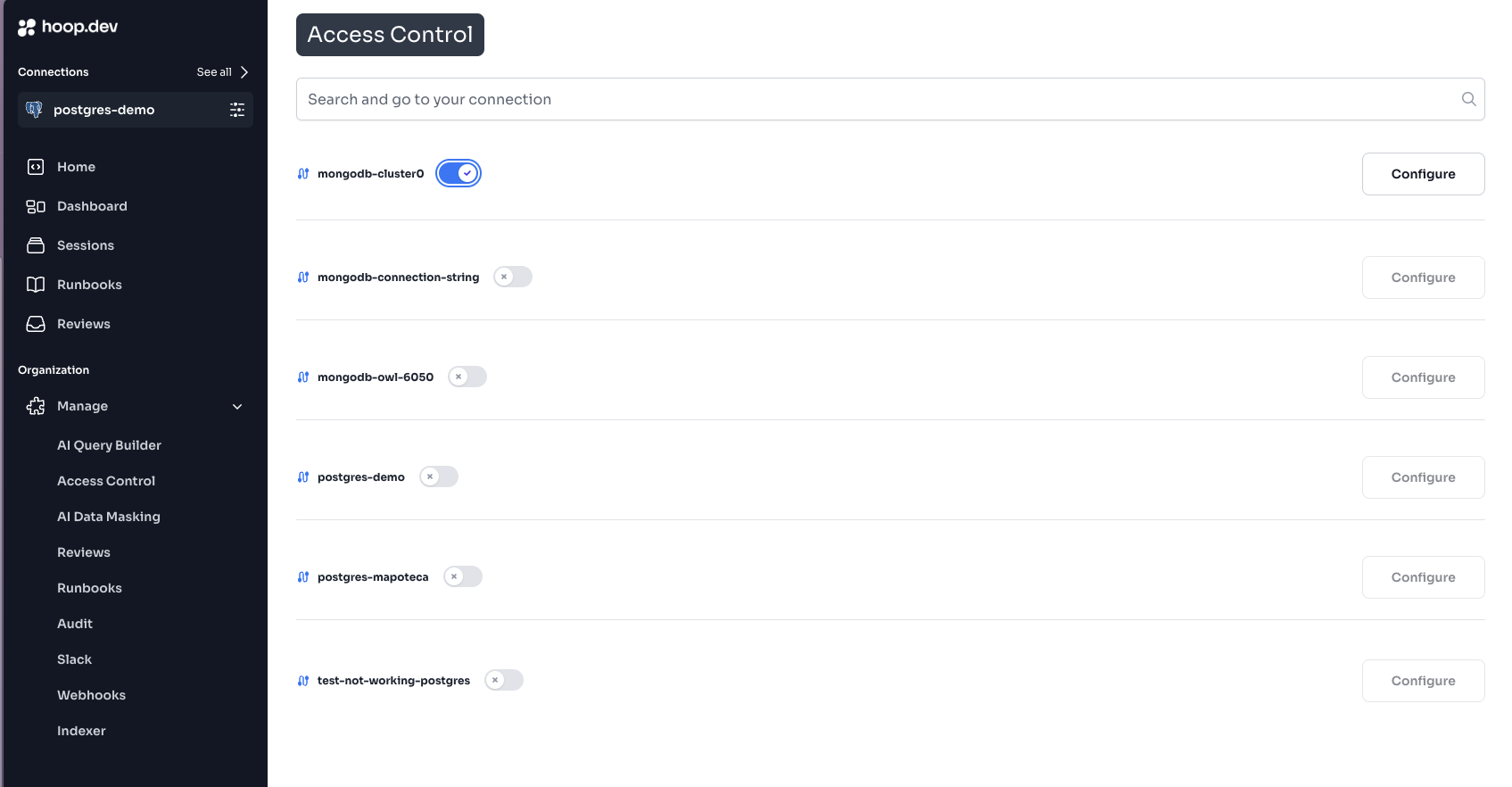
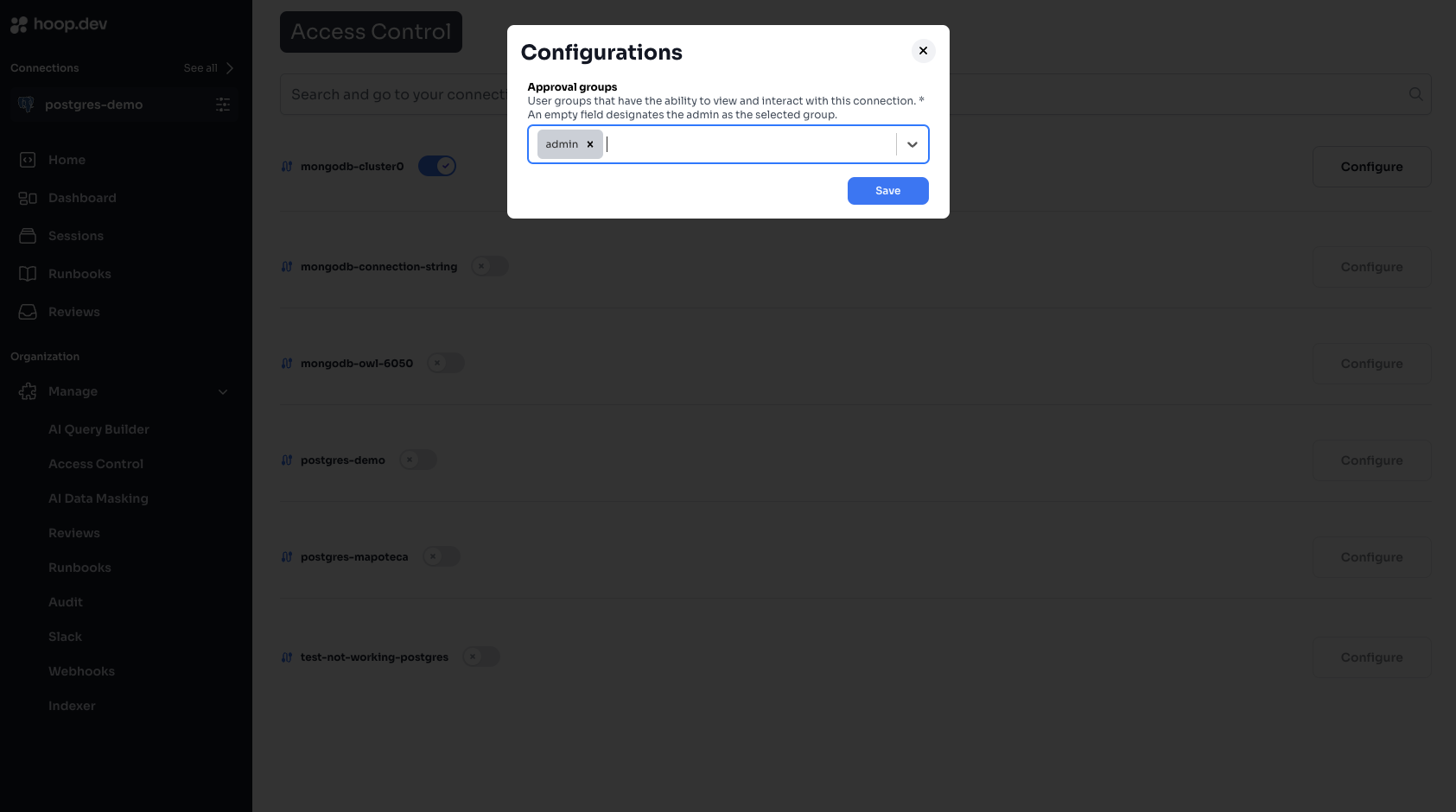
Step 2: Configure Connection Access
Step 3: Verify Access
- Log in as a user in one of the allowed groups
- Verify you can see and access the connection
- Log in as a user NOT in the allowed groups
- Verify the connection is not visible
Managing Groups
Creating Groups
Groups are typically managed in your identity provider (Okta, Auth0, Azure AD, etc.). When users log in, their group memberships are synced to Hoop. In Hoop, you can also create groups manually:- Go to Manage > Users & Groups
- Click Create Group
- Enter a group name (e.g.,
prod-access) - Add users to the group
Syncing Groups from Identity Provider
Configure your identity provider to include groups in the ID token:- Add a
groupsclaim to your OIDC configuration - Map your IdP groups to Hoop groups
- See Identity Provider Configuration for detailed setup
Built-in Roles
| Role | Description |
|---|---|
admin | Full access to all connections and settings |
auditor | Read-only access to sessions and audit logs |
Admin users bypass Access Control and can access all connections. Use admin sparingly.
Common Patterns
Pattern 1: Environment-Based Access
Restrict production access to senior team members:| Connection | Allowed Groups |
|---|---|
| prod-db | senior-engineers, dba |
| staging-db | engineering |
| dev-db | engineering, contractors |
Pattern 2: Team-Based Access
Each team only sees their own resources:| Connection | Allowed Groups |
|---|---|
| payments-db | payments-team |
| inventory-db | inventory-team |
| analytics-db | analytics-team, data-science |
Pattern 3: Role-Based Access
Different access levels for different roles:| Connection | Allowed Groups |
|---|---|
| prod-db-readwrite | dba |
| prod-db-readonly | engineering, support |
| prod-db-analytics | analytics |
Pattern 4: Contractor Access
Temporary access for external contractors:- Create a
contractorsgroup - Add contractors to the group
- Only allow
contractorsgroup on specific, limited connections - Remove from group when contract ends
Combining with Other Features
Access Control works with other Hoop security features:| Feature | Combined Behavior |
|---|---|
| Access Requests | Users in allowed groups can request access; others can’t |
| Guardrails | Allowed users still subject to query restrictions |
| Live Data Masking | Allowed users see masked data |
| Session Recording | All access is audited regardless of permissions |
Example: Layered Security
For a production database:- Access Control: Only
senior-engineerscan see the connection - Access Requests: Require JIT approval before connecting
- Guardrails: Block
DROP TABLEandDELETEwithout WHERE - Live Data Masking: Redact PII in query results
- Session Recording: Log all queries for audit
Troubleshooting
User Can’t See a Connection
Check:- Access Control is enabled on that connection
- User’s groups are in the allowed list
- User has logged out and back in (to sync groups)
- Identity provider is sending the
groupsclaim
- Go to Manage > Users
- Find the user and click to view details
- Check their group memberships
User Sees Connection But Can’t Connect
This is likely an Access Request or Guardrail issue, not Access Control. Check:- Is JIT or Action Access Request enabled?
- Are there Guardrails blocking the connection?
Groups Not Syncing from IdP
Check:groupsclaim is configured in your IdP- The OIDC scope includes
groups - Gateway environment variables are correct
- See Identity Provider Configuration
Best Practices
Least Privilege
Grant minimum access needed for each role
Use Groups, Not Users
Assign access to groups, not individual users
Regular Audits
Review access permissions quarterly
Document Policies
Write down who should have access to what
Access Review Checklist
Quarterly, review:- Are all group memberships still appropriate?
- Are there users who left but still have access?
- Are there connections that should have stricter access?
- Are contractors’ access limited to their engagement period?
Next Steps
Configuration Guide
Detailed configuration options
Identity Providers
Set up SSO and group sync
Access Requests
Add approval workflows
Guardrails
Block dangerous operations